�������: 1-15 ���鵽��AES����ؼ�¼416�� . ��ѯʱ��(0.108 ��)
FIB-AES-TEM-EELS���ü������϶����������Ʒ�о��е�Ӧ�ã�ͼ��
FIB-AES-TEM-EELS ���ü��� �϶���� ������Ʒ�о�
2023/4/4
Flush+Reload��������Cache�ṹ���������ŵ�,�ڼ����㷨ִ��·���Ͻ���ָ��������OpenSSL0.9.8.b��AES���ܴ���ʵ��,�����������ʵ�ֵı���������һ�μ���ֻʹ��һ��Te4��,�����һ�����AES���һ�ּ���ʵʩFlush+Reload�����ķ�����ʵ�������������ռ�280��10��3��AES�������ĺͼ�ʱ���ݺ�,ͨ������ֵ������ֵ���������,�ҵ����Ĺ��н�ɵõ����һ...
SPAE a mode of operation for AES on low-cost hardware
secret-key cryptography AES block ciphers
2019/9/16
We propose SPAE, a single pass, patent free, authenticated encryption with associated data (AEAD) for AES. The algorithm has been developped to address the needs of a growing trend in IoT systems: sto...
A Key-Independent Distinguisher for 6-round AES in an Adaptive Setting
SPN AES Exchange Attack
2019/8/20
In this paper, we study the results of the recently proposed exchange attack in an adaptive setting. As expected, it leads to present a better 6-round key-independent distinguisher in terms of data an...
����������ѧ���������μ�9-10 AES��Դ���ۡ�
Invariant subspaces (Crypto'11) and subspace trails (FSE'17) are two related recent cryptanalytic approaches that led to new results on, e. g. PRINTCipher and AES. We extend the invariant subspace app...
Reducing the Cost of Implementing AES as a Quantum Circuit
quantum cryptanalysis quantum circuit Grover��s algorithm AES
2019/7/24
To quantify security levels in a post-quantum scenario, it is common to use the quantum resources needed to attack AES as a reference value. Specifically, in NIST��s ongoing post-quantum standardizatio...
In this short report we present a short linear program for AES MixColumn with 94 XOR gates.
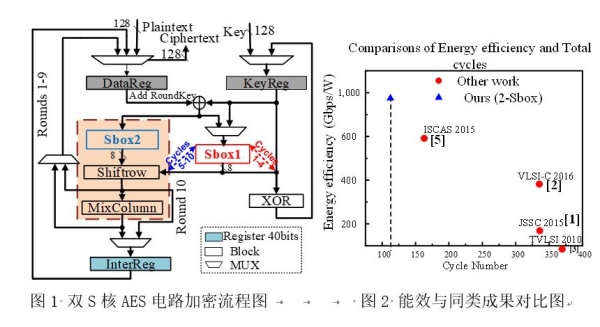
���ϴ�ѧ��ΰΰ������Ŷ���2019 Symposia VLSI Technology and Circuits���ʻ��鷢������ЧAES��·�ɹ���ͼ��
���ϴ�ѧ ��ΰΰ ��� 2019 ����Ч AES��·
2019/8/8
2019��6��9��14�գ����ӿ�ѧ�빤��ѧԺ��ΰΰ���ڡ�������ڵȸ��ձ��μ�Symposia VLSI Technology and Circuits���顣��ΰΰ������Symposium on VLSI Circuits�ֻ��C20 session�����棬����Ϊ��A 923Gbps/W, 113-Cycle, 2-Sbox Energy-efficient AES Accelerator in 2...
New Circuit Minimization Techniques for Smaller and Faster AES SBoxes
AES SBox circuit area circuit depth
2019/7/15
In this paper we consider various methods and techniques to find the smallest circuit realizing a given linear transformation on nn input signals and mm output signals, with a constraint of a maximum ...
This works studies the use of the AES block-cipher for Picnic-style signatures, which work in the multiparty-computation-in-the-head model. It applies advancements to arithmetic circuits for the compu...
Dissecting the CHES 2018 AES Challenge
AES CTF
2019/7/10
One challenge of the CHES 2018 side channel contest was to break a masked AES implementation. It was impressively won by Gohr et al. by applying ridge regression to obtain guesses for the hamming weig...
In this paper we investigate the security of 5-round AES against two different attacks in an adaptive setting. We present a practical key-recovery attack on 5-round AES with a secret s-box that requir...
Mixture Integral Attacks on Reduced-Round AES with a Known/Secret S-Box
AES Mixture Differential Cryptanalysis Secret-Key Distinguisher
2019/7/8
The starting point of our work is ��Mixture Differential Cryptanalysis�� recently introduced at FSE/ToSC 2019, a way to turn the ��multiple-of-8�� 5-round AES secret-key distinguisher presented at Eurocry...
Scrutinizing the Tower Field Implementation of the $\mathbb{F}_{2^8}$ Inverter -- with Applications to AES, Camellia, and SM4
Tower field Inverter S-box
2019/6/24
The tower field implementation of the F28F28 inverter is not only the key technique for compact implementations of the S-boxes of several internationally standardized block ciphers such as AES, Camell...
�й��о����������а�-��
- ���ڼ���...
�й�ѧ���ڿ����а�-��
- ���ڼ���...
�����ѧ���л������а�-��
- ���ڼ���...
�й���ѧ���а�-��
- ���ڼ���...
�ˡ���-ƪ
- ���ڼ���...
�Ρ���-ƪ
- ���ڼ���...
��������-ƪ
- ���ڼ���...
�������� -ƪ
- ���ڼ���...
֪ʶҪ��-ƪ
- ���ڼ���...
���ʶ�̬-ƪ
- ���ڼ���...
��������-ƪ
- ���ڼ���...
ѧ��ָ��-ƪ
- ���ڼ���...
ѧ��վ��-ƪ
- ���ڼ���...


